Elliptic curve cryptography explained: How ECC works, why it matters, and where it’s used
As digital communication expands across devices and networks, the need for efficient and reliable encryption continues to grow. Elliptic curve cryptography (ECC) has become a standard solution due to its ability to deliver strong security with reduced computational cost. It is now embedded in many widely used technologies and protocols.
In this guide, we'll look at how ECC works, where it's used, why it's useful, and where its limits begin to show.
What is elliptic curve cryptography?
ECC is a form of public-key cryptography, also known as asymmetric encryption. It allows systems to create secure connections and verify digital signatures.
Its main advantage is that ECC delivers strong security with much smaller keys than older systems like Rivest–Shamir–Adleman (RSA). That often makes it faster and lighter, which is why it’s common in phones, websites, messaging apps, and cryptocurrencies.
How ECC fits into public key cryptography
ECC operates within the public-key model, which means it uses a matched pair of keys rather than a single shared secret. One key is public and can be shared openly; the other stays private. This setup lets two parties establish trust over the internet without meeting in person or exchanging secrets through a secure channel beforehand.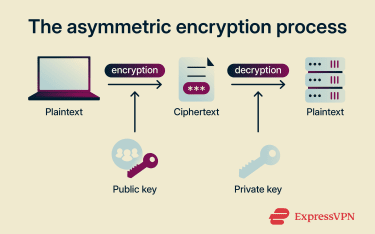
Say Alice wants to send Bob a private message over the internet. To do this, she asks Bob for his public key. Bob shares it freely: that's the whole point of a public key. Alice then uses it to encrypt her message, turning readable text into unreadable ciphertext. She sends the ciphertext to Bob, who decrypts it with his private key, a key only he possesses.
The result is that Alice's message reaches Bob securely, and anyone who intercepts it along the way sees only scrambled data they can't decode.
This works because the two keys are mathematically linked but not interchangeable. The public key locks the message; only the matching private key can unlock it. That's why the private key must stay secret; whoever holds it can decrypt anything encrypted with the corresponding public key.
How does elliptic curve cryptography work?
At its core, ECC relies on an operation that's easy to perform in one direction but practically impossible to reverse.
Elliptic curve multiplication explained
An elliptic curve is a specific type of equation whose solutions, when plotted, form a curve with useful mathematical properties. In cryptography, these curves are defined over finite fields, meaning the calculations stay within a fixed range of values rather than spanning infinite possibilities.
Every ECC system starts with a publicly known point on the curve, called the generator point (G). The core operation in ECC is scalar multiplication: picking a number and adding G to itself that many times, following the curve's geometric rules for point addition. The result is another point on the curve.
To create a key pair, a user picks a random number (d) as their private key, then performs scalar multiplication to get the public key (Q).
The relationship is Q = [d]G, meaning Q is obtained by adding G to itself d times.
Here's what makes this secure. Given G and d, calculating Q is quick. But given G and Q, finding d is computationally infeasible. The best-known methods would take longer than the age of the universe for a sufficiently large curve. This is called the elliptic curve discrete logarithm problem (ECDLP), and it's the mathematical foundation of ECC's security. It's what allows the public key to be shared openly while keeping the private key safe.
Public and private keys in ECC
The private key is a random number chosen from an allowed range for the selected curve. The public key is the point on the curve derived from that number through scalar multiplication.
Because the public key comes from a one-way operation, anyone can use it in a protocol, but only the holder of the private key can complete certain actions, like producing a valid digital signature.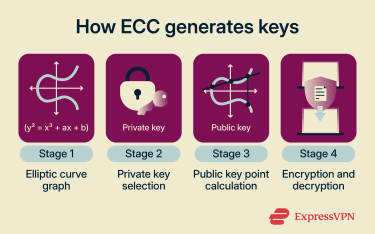
How ECC supports encryption and digital signatures
ECC is most commonly used for two purposes: key exchange and digital signatures. For encrypting actual data, it's typically paired with a symmetric cipher like Advanced Encryption Standard (AES).
This division exists because asymmetric encryption is computationally expensive for large amounts of data. Instead, ECC helps two parties agree on a shared secret, and that secret is then used with a fast symmetric algorithm to encrypt the content.
In practice, a secure connection might work like this:
- Handshake: The client and server use Elliptic Curve Diffie-Hellman Ephemeral (ECDHE) to agree on a shared session secret. "Ephemeral" means the keys are generated fresh for each session, which provides forward secrecy.
- Data transfer: The session secret is used with AES to encrypt application data.
In short, ECC opens the secure door; AES protects what passes through it.
ECC vs. RSA: What are the key differences?
ECC and RSA are both widely used forms of public-key cryptography, but they rely on different math and make different tradeoffs.
| ECC | RSA | |
| Mathematical foundation | Elliptic curve discrete logarithm problem | Integer factorization |
| Key size for similar security | Smaller (e.g., 256-bit) | Larger (e.g., 3072-bit) |
| Efficiency | Less data and processing power | More data and processing power |
| Performance | Better fit for high-volume or resource-limited systems | Heavier, especially at higher security levels |
| Compatibility | Common in newer systems | Strong legacy support |
| Common use cases | Secure web traffic, messaging apps, mobile devices, cryptocurrencies | Older systems, legacy enterprise environments |
| Best fit | When efficiency and smaller keys matter | When backward compatibility matters most |
Mathematical foundation
RSA and ECC both rely on math problems that work in one direction but are nearly impossible to reverse.
With RSA, security comes from integer factorization. Multiplying two large prime numbers together is easy. But if you only have the result, figuring out which two primes produced it is extremely difficult, and that difficulty grows as the numbers get larger.
With ECC, security comes from the ECDLP, which we covered earlier. Both approaches create a one-way operation, but ECC achieves it with smaller numbers, which is why ECC keys can be shorter for the same level of security.
Performance and efficiency
Because ECC uses smaller keys, it requires less storage, less bandwidth, and less processing power to achieve the same security level. This makes a practical difference for websites handling heavy traffic, mobile apps where battery life matters, and Internet of Things (IoT) devices with limited resources.
That said, performance depends on the specific system, software, and task. ECC isn't universally faster in every scenario, but for most modern use cases, it's the more efficient choice.
Adoption, compatibility, and use cases
RSA has been around since 1977, so it remains embedded in older systems and enterprise environments where backward compatibility is essential. If an organization needs to support legacy infrastructure, RSA may still be the practical choice.
ECC is now the default in most modern systems. For new implementations without legacy constraints, ECC is typically the better fit.
Real-world applications of elliptic curve cryptography
ECC is built into many of the systems people use every day to browse securely, send messages, approve transactions, and prove identity online.
Cryptocurrencies and blockchain
Bitcoin is one of the clearest real-world examples of ECC in use. It uses an ECC-based digital signature method to verify transactions, letting the network confirm that the person spending funds controls the right private key, without exposing that private key itself.
This is why ECC works well in blockchain systems. Public keys and digital signatures need to be shared, checked, and stored across a large network. ECC makes that practical by offering strong security with relatively small keys and signatures.
Mobile devices and secure messaging
ECC is widely used in secure messaging apps like WhatsApp and Signal. It helps establish a protected connection between users before messages are encrypted and sent.
Mobile devices have limited battery power, memory, and processing capacity, so security has to be efficient, not just strong. ECC fits well here because it delivers protection without noticeable lag, heavy battery drain, or extra steps. The cryptography does important work in the background, but the app still feels quick and responsive.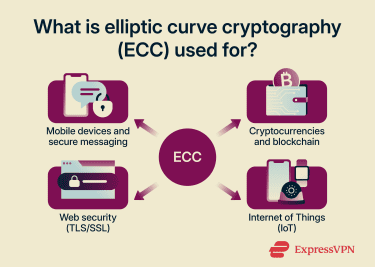
TLS, SSL, and digital certificates
ECC often helps protect secure web browsing. The current protocol is Transport Layer Security (TLS), though many people still say Secure Sockets Layer (SSL) out of habit.
When you open a secure website, ECC can help set up the connection, support the key exchange, and play a role in the digital certificates that confirm you're talking to the right site. That's why ECC is closely tied to everyday online security, even for people who never hear its name.
Learn more: SSL vs. TLS: Key differences and why TLS is better
Internet of Things (IoT)
IoT devices (smart home gadgets, wearables, connected cars, industrial sensors, etc.) often have tight constraints: limited battery, memory, and processing power. They still need strong security, but they can't handle the same demands as larger computers or servers.
ECC is a natural fit here. It provides strong protection with smaller keys and less processing overhead, letting these devices stay secure without draining resources or slowing down.
What are the limitations of ECC?
For all its strengths, ECC has real-world challenges:
- It’s difficult to implement correctly: ECC math is less intuitive than RSA's. That makes implementation mistakes more likely, particularly in key generation, signature validation, random number handling, and side-channel protections.
- Small mistakes can break security entirely: If the random number used in an ECC signature is weak or reused, the private key can be exposed.
- It’s vulnerable to side-channel attacks: Even when the math is implemented correctly, attackers may recover keys by measuring timing, power consumption, electromagnetic emissions, or cache behavior. Defending against these attacks requires careful, constant-time code.
- Curve choice matters: Not all elliptic curves are equally trusted or practical. After reports emerged in 2013 that the U.S. National Security Agency (NSA) had inserted a backdoor into a National Institute of Standards and Technology (NIST)-recommended random number generator (Dual_EC_DRBG), some cryptographers raised concerns about how NIST's standard curves were selected. Alternatives like Curve25519 were designed with transparent, verifiable parameters to address these concerns.
- Compatibility can be uneven: Modern systems widely support ECC, but older devices, legacy software, and some embedded environments may have limited or inconsistent support.
- It doesn't work alone: ECC handles key exchange and digital signatures. For encrypting actual data, it still needs to work alongside symmetric encryption (like AES), hashing, certificate management, and secure protocols.
Why quantum computers threaten ECC
Current quantum computers can't break ECC. But a sufficiently powerful one could. The threat comes from Shor's algorithm, developed by mathematician Peter Shor in 1994. It shows that a quantum computer with enough stable qubits could efficiently solve the ECDLP. If that becomes possible, an attacker could derive private keys from public keys.
This threat isn't unique to ECC. Shor's algorithm would also break RSA and any cryptography based on factoring large numbers or solving discrete logarithms. Researchers have already found a way to factor a 2048-bit RSA key in merely 8 hours (rather than trillions of years) by using a quantum computer.
That's why researchers and standards bodies are developing post-quantum cryptography (PQC): algorithms designed to resist attacks from both classical and quantum computers. In 2024, NIST finalized its first post-quantum standards, marking a major step toward real-world adoption.
The transition won't happen overnight. Many systems are expected to go through a hybrid phase, running ECC alongside post-quantum algorithms. That way, they remain protected by ECC today while adding quantum resistance for the future.
FAQ: Common questions about elliptic curve cryptography
Is ECC more secure than RSA?
How does ECC compare to AES?
Is ECC a cipher?
Why is ECC more efficient than RSA?
How does ECC benefit mobile devices?
Does Bitcoin use RSA or ECC?
Can ECC be broken by quantum computers?
What are the main advantages of using ECC?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN