Expressvpn Glossary
Traffic shaping
What is traffic shaping?
Traffic shaping (or packet shaping) is a network bandwidth management technique used to control the flow of data across a network connection. It works by delaying or queuing out lower-priority data packets while allowing business-critical or time-sensitive traffic, like Voice over Internet Protocol (VoIP), to pass first.
By pacing data transmission and smoothing sudden traffic bursts, traffic shaping reduces congestion, improves consistency, and ensures fairer distribution across users and applications. It is a core component of Quality of Service (QoS) implementations.
How does traffic shaping work?
Unlike traffic policing, which drops packets that exceed a set threshold, traffic shaping temporarily buffers excess packets and sends them later. This helps smooth out bursts of traffic and reduces packet loss on congested links.
The process begins with traffic classification. The network system examines each packet and groups it according to criteria such as application type, port number, protocol, IP address, or virtual local area network (VLAN) tag. This classification determines how the packet will be treated as it moves through the network.
Next, packets are placed into queues rather than being transmitted immediately. Traffic shaping releases packets from these queues at controlled intervals to prevent sudden spikes in traffic that could overwhelm a network link.
To control how packets leave the queue, traffic shaping relies on rate-control algorithms. One commonly used method is the token bucket algorithm, which allows controlled bursts of traffic up to a predefined threshold. In this model, a bucket fills with tokens at a steady rate, and each packet must consume a token before it can be transmitted. If the bucket runs out of tokens because traffic exceeds the configured rate, packets must wait until more tokens become available. Another approach is the leaky bucket algorithm, which releases packets at a constant, fixed rate to create a smoother and more predictable traffic flow.
Traffic shaping can also apply fair queuing mechanisms that ensure multiple traffic flows share bandwidth more evenly. In many cases, latency-sensitive traffic such as voice or video calls is given higher priority to maintain performance.
Finally, administrators can enforce rate limits on specific network interfaces or traffic classes. These limits prevent a single user, device, or application from consuming all available bandwidth and degrading performance for others on the same network.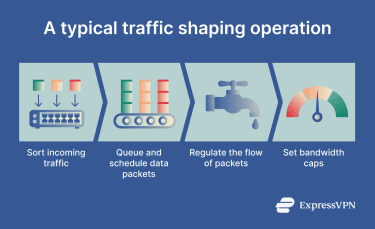
Why is traffic shaping important?
Some of traffic shaping key benefits include:
- Lowering jitter for real-time applications, such as video and online calls.
- Keeping critical apps responsive under load.
- Preventing bandwidth monopolization.
- Enforcing performance targets and service-level agreements (SLAs).
- Supporting differentiated service tiers in internet service provider (ISP) environments.
- Reducing the impact of distributed denial-of-service (DDoS) attacks.
Where is traffic shaping used?
Traffic shaping is used in environments where bandwidth is shared and predictable performance is required.
- ISPs: ISPs shape traffic during busy times to maintain baseline performance for all users.
- Enterprise networks: Organizations use shaping on corporate infrastructure to prioritize critical apps.
- Data centers: Traffic shaping controls east-west (server-to-server) traffic flows to prevent internal congestion and ensure predictable app performance.
- Retail and branch networks: Stores prioritize checkout and payment traffic over less critical data like guest Wi-Fi.
- Virtual private network (VPN) gateways: VPN concentrators apply shaping to manage bandwidth fairly across multiple tunnels.
Risks and privacy concerns
Even though traffic shaping can help manage networks better, it has certain challenges:
- Perceived throttling: When an ISP slows specific traffic types to manage networks, users can experience sluggish service that feels like throttling rather than neutral management.
- Deep packet inspection (DPI): Some shaping systems rely on inspecting packet headers and metadata to classify traffic. This raises privacy concerns, and the process can expose sensitive information like user identifiers.
- Policy bias or misconfiguration: Poorly designed shaping policies may inadvertently favor certain users or apps over others. Misconfiguration can also introduce latency and buffering, worsening the performance problems the system was intended to solve.
- Traffic fingerprinting: Even without DPI, timing and volume patterns in shaped traffic can be used to infer app use or user behavior.
Further reading
- Deep packet inspection (DPI): How it works and why it matters
- What is packet loss? Everything you need to know
- What is network jitter, and how does it impact internet performance?
- How to fix packet loss for a stable connection

