Expressvpn Glossary
DNS tunneling
What is DNS tunneling?
Domain Name System (DNS) tunneling is the practice of carrying non-DNS data inside DNS queries and responses. It relies on the fact that DNS traffic is often allowed through networks because DNS is necessary for name resolution, and in some environments, it may receive less scrutiny than other protocols.
Attackers primarily use DNS tunneling in command-and-control (C2) operations or data exfiltration attacks to communicate with malware running on an infected device. DNS tunneling can also be used legitimately for testing or specialized administrative purposes, though in security contexts, it's most often discussed as a malicious technique.
How does DNS tunneling work?
Once malware infects the target device, a DNS tunneling attack typically unfolds as follows:
- The attacker registers a domain on a server they control.
- The malware encodes data and sends it in DNS queries to that domain, mimicking normal DNS traffic.
- A DNS resolver performs a lookup and forwards the request until it reaches the attacker’s authoritative server.
- The attacker's server decodes the request and returns a response containing new commands or data.
- The malware decodes the response and executes the instructions.
Attackers repeat this cycle for as long as the malware persists on the device, sending small amounts of data each time to blend in with normal DNS traffic and avoid triggering detection.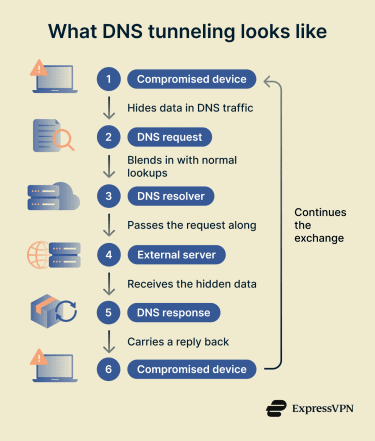
Where is DNS tunneling used?
DNS tunneling has both legitimate and malicious uses, including:
- Red team simulations and penetration tests: Security teams can use it in controlled environments to test whether network monitoring and filtering tools can detect and block tunneled traffic.
- Malware C2: Attackers may use it to send instructions to compromised devices and receive data while blending in with normal DNS traffic
- Data exfiltration: Cybercriminals may use it to extract small amounts of sensitive data from restricted networks.
- Working around network restrictions: DNS tunneling software has sometimes been used in environments where DNS traffic is allowed before broader network access is granted, such as some captive portals or restrictive firewall setups.
Why is DNS tunneling dangerous?
DNS tunneling can be hard to detect because attackers hide small amounts of data inside routine DNS traffic, allowing compromised systems to communicate while blending in with normal network activity. The technique abuses DNS, which most networks rely on for everyday internet access, so organizations often need to monitor and filter it rather than block it outright.
It can affect any network that allows DNS queries from endpoints if an attacker gains access to a device and uses DNS for C2 or data exfiltration. Detection depends on visibility into DNS logs and query patterns, and encrypted DNS methods such as DNS over HTTPS (DoH) can make monitoring harder when appropriate controls are not in place.
Further reading
- DNS security: How to protect your network from DNS threats
- The ultimate guide to recursive DNS
- Types of DNS servers: Everything you need to know
- DNS record types explained: A complete guide for privacy
- Complete guide to understanding managed DNS

