Expressvpn Glossary
256-bit encryption
What is 256-bit encryption?
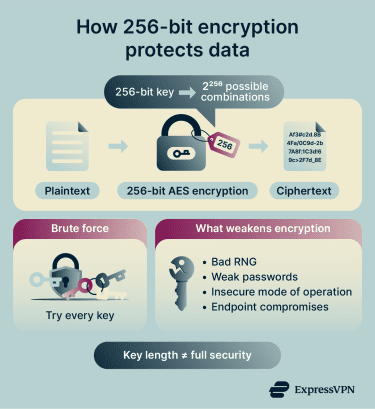
256-bit encryption is a cryptographic method that uses a 256-bit key to encrypt and decrypt data. This results in 2²⁵⁶ possible key combinations, making brute-force attacks impractical with current computing capabilities.
One of the most widely used 256-bit encryption standards is the Advanced Encryption Standard (AES), particularly 256-bit AES. However, other algorithms, such as XChaCha20, also support 256-bit keys.
How does 256-bit encryption work?
 The way 256-bit encryption works can vary depending on the specific algorithm being used. Its strength and efficiency also depend on the algorithm’s design and on how securely the key is generated and managed.
The way 256-bit encryption works can vary depending on the specific algorithm being used. Its strength and efficiency also depend on the algorithm’s design and on how securely the key is generated and managed.
The general workflow typically follows these steps:
- The system generates a 256-bit key.
- The system encrypts data through a series of mathematical operations to produce a ciphertext. The exact number depends on the algorithm design and key size.
- The receiver decrypts the ciphertext using the appropriate key.
Where is it used?
256-bit encryption protects sensitive data in:
- Virtual private networks (VPNs) and secure network protocols.
- HTTPS websites via Transport Layer Security (TLS).
- Full-disk and file encryption tools.
- Password manager vaults.
- Secure cloud storage services.
- High-security or regulated environments, such as government and military systems.
- Messaging apps, such as WhatsApp, Signal, and Facebook Messenger.
Why is 256-bit encryption important?
256-bit encryption helps secure data at rest and in transit. It can help organizations:
- Protect sensitive information against brute-force attacks.
- Support compliance with data protection standards.
- Maintain strong long-term cryptographic resilience, including against potential future quantum threats.
Note: Quantum algorithms like Grover’s algorithm could theoretically reduce the brute-force complexity of 256-bit AES to ~128 bits (or from 2²⁵⁶ to approximately 2¹²⁸ operations).
Even with this reduction, the effort required remains computationally impractical, meaning 256-bit AES is still considered secure against current quantum threats.
Risks and privacy concerns
Although 256-bit encryption is highly secure, security can be weakened by poor implementation or system vulnerabilities:
- Weak passwords: Easy-to-guess passwords used for key derivation may allow attackers to reproduce decryption keys.
- Poor random number generation (RNG): Low-entropy randomness can make encryption keys easier to predict. Secure systems rely on cryptographically secure random number generators (CSPRNGs).
- Misconfiguration: Weak or inappropriate modes of operation may reduce encryption strength.
- Side-channel attacks: Analysis of signals such as timing or power usage may expose cryptographic keys.
- Endpoint compromise: Access to a device where data is decrypted may allow attackers to read the plaintext.
Further reading
- What is AES encryption?
- What is 128-bit encryption, and is it still secure?
- What is data encryption?
- Encryption protocols explained: What they are and how they work
- What is ChaCha20, and how does it work?

