What is cyberwarfare and why does it matter?
Digital systems now sit at the center of government, military, and economic activity, making networks and data an increasingly important arena for competition and conflict. Cyber incidents can carry strategic intent, involve state-linked actors, and produce real-world disruption at scale.
While the topic is complex and has no international consensus, understanding the general principles of cyberwarfare matters because it clarifies how these operations differ from ordinary crime, why attribution and intent are often contested, and how effects can spill over into private organizations and public life.
What is cyberwarfare?
Cyberwarfare is generally understood as the use of cyber operations by a state (or state-directed actors) against another state or its interests to achieve strategic or military objectives, sometimes alongside conventional diplomacy or armed conflict.
There is no single internationally accepted definition. Governments and experts disagree on where to draw the line between espionage, sabotage, and cyber activity that could be treated as a use of force and potentially trigger a military response.
Key players: Nation-states, hacktivists, and cyber mercenaries
The primary players in cyberwarfare are nation-states: governments that use cyber operations to advance national objectives. In practice, nation-state activity can include both official government units (for example, within intelligence, security, or military structures) and state-linked actors who operate with government direction, support, or tolerance.
Such actors are state-sponsored hacking groups: teams assessed to work for, or closely alongside, a government. They are typically organized around long-term state objectives and may operate either inside government institutions or through affiliated networks that support government priorities.
These groups are often described as advanced persistent threats (APTs), a term referring to adversaries that pursue objectives over extended periods, adapt to defenders, and seek to maintain access to execute their objectives.
States may also turn to cyber mercenaries: commercial providers that sell offensive cyber capabilities or services to clients, often including government agencies. These firms operate as private businesses, but their work can serve state objectives when governments purchase, contract, or otherwise rely on their capabilities.
Beyond state-directed and commercially hired actors, cyber conflicts can also involve hacktivists: individuals or groups motivated primarily by political, ideological, or social causes rather than profit. Hacktivist activity is often framed as activism, but it can still escalate tensions or contribute to conflict dynamics when it targets states or state-linked interests.
Learn more: Read our detailed guide on nation-state cyber actors: who they are and why they matter.
Types of cyberwarfare attacks
Cyberattacks are carried out for a broad and shifting set of objectives, so there is no universally fixed list of “types of cyberwarfare.” However, several goals and techniques recur frequently in state conflict and state-linked activity.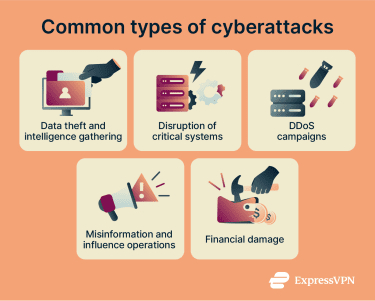
Espionage and surveillance
Espionage focuses on covert access to sensitive information to gain strategic, political, military, or economic advantage. It commonly targets government, defense, and high-value industrial or research organizations and can involve prolonged access to monitor activity and collect data.
Techniques often associated with cyber espionage include exploiting previously unknown vulnerabilities (zero-day attacks), intercepting communications, and deploying surveillance-oriented malicious code.
Sabotage and infrastructure disruption
Sabotage aims to create operational effects by degrading, disabling, or manipulating systems that support real-world processes and essential services, rather than primarily collecting information.
Industrial control systems and other operational technology (OT) are important targets in this category because they support critical infrastructure and have unique constraints (performance, reliability, and safety) that can make security upgrades harder to implement without operational tradeoffs.
Disruption of OT environments can cause service outages, force shutdowns, or create unsafe system conditions, with cascading economic and societal consequences when essential services are affected.
Denial-of-service (DoS) and distributed DoS (DDoS)
A denial‑of‑service (DoS) attack attempts to overwhelm a network or system so it can’t handle legitimate traffic. In a distributed DoS (DDoS) attack, attackers use botnets (large networks of compromised devices) to send floods of traffic from multiple sources.
These network attacks can cause outages that last for extended periods of time, while the DDoS campaign itself can be perpetuated for months or even years and be powered by a massive web of bots.
Propaganda and psychological operations
Information operations aim to shape how audiences understand events, make decisions, or trust institutions. Online platforms can amplify these efforts by enabling rapid, wide distribution of messages, targeted outreach to specific communities, and coordinated amplification, sometimes through networks that misrepresent who is behind the activity.
Economic disruption and data theft
Some cyber operations focus on damaging economic activity or extracting valuable data through theft of financial information, disruption of business operations, or interference with supply chains and market-related systems.
The International Monetary Fund (IMF) has warned that cyber incidents pose rising financial-stability concerns. It reports that “extreme losses” from cyber incidents have more than quadrupled since 2017 to about $2.5 billion.
Technologies and tools used in cyberwarfare
Cyberwarfare relies on a range of tools, from malware and ransomware to AI‑enabled automation. Understanding these technologies helps organizations recognize threats and evaluate defenses.
Malware, ransomware, and spyware
“Malware” is the catch-all term for software intentionally created to cause harm or perform unwanted actions on a system. Two common malware families are ransomware and spyware.
Ransomware is designed to lock up data or systems (most often by encrypting files) and then demand payment or other concessions to restore access. Spyware is designed to be installed secretly so it can collect information about individuals or organizations without their knowledge.
In real-world operations, these categories can blur. A single incident may involve multiple goals, such as gathering information first and then using ransomware to disrupt operations or increase pressure.
Malware also needs a way to reach a target. Common delivery methods include phishing (deceptive messages that push malicious links or attachments) and web-based delivery, such as compromised sites and drive-by downloads.
AI and machine learning in cyber offense
AI is increasingly discussed as a force multiplier for cyber operations because it can reduce time and effort for tasks such as content generation, analysis, and workflow automation, which can increase the scale and tempo of certain offensive activities.
Recent public assessments like the European Union Agency for Cybersecurity (ENISA) Threat Landscape 2025 also highlight AI-enabled impersonation and deepfakes as an evolving risk area, particularly for social engineering and fraud-like targeting at a higher volume.
Botnets and command-and-control servers
A botnet is a network of compromised devices infected with malware and controlled remotely. Cybercriminals infect targets with various viruses to breach their computers, take control of systems, and organize them into a network of bots.
These bots connect to a command-and-control (C2) server, which sends commands and receives stolen data. Botnets are used for DDoS attacks, spam, and ransomware distribution, but they can also be used for cybersecurity defense by simulating real-world attack traffic.
Because they span thousands of devices, attributing the attack to a specific person or group is difficult. Defenders counter botnets by disrupting C2 infrastructure, patching vulnerabilities, and collaborating with providers to shut down malicious traffic.
Cyberwarfare vs. traditional warfare
Both cyberwarfare and traditional warfare are used to pursue political or military objectives. The main difference is the domain: traditional warfare relies on physical force, while cyberwarfare uses operations in and through digital systems.
Key differences and overlaps
Cyberwarfare differs from traditional warfare in several ways. It enables remote action across borders without moving forces into the target’s territory, and it can be highly asymmetric, allowing comparatively smaller actors to impose meaningful costs on stronger opponents.
Attribution is also harder than in many kinetic contexts. Actors can route activity through third-party infrastructure, use proxies, and hide technical fingerprints, so public attribution is often presented as an assessment rather than a simple proof.
Cyber operations may disrupt services without immediate visible destruction, but they can still have serious consequences, especially when they affect OT and industrial control systems that interact with the physical world (for example, systems that support essential services).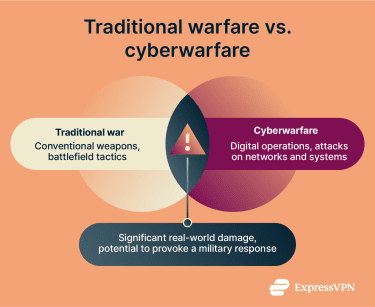
Cyberwar is often discussed as a state-on-state activity that could, in some circumstances, trigger military responses, but there is no universally accepted threshold for when a cyber incident becomes an “armed attack” under international law.
Legal and ethical considerations
International law applies to state conduct in cyberspace, including the United Nations (UN) Charter framework on the use of force and self-defense, but how those rules apply to specific cyber operations continues to develop through state practice and legal interpretation.
The Tallinn Manual is an influential but non-binding expert analysis of how international law may apply to cyber operations. It argues that a cyber operation may amount to a prohibited “use of force” and, in some cases, may implicate self-defense when its scale and effects are comparable to kinetic uses of force.
Many incidents fall below those thresholds and still occur frequently. This is one reason states often rely on a mix of diplomatic, legal, technical, and (where applicable) countermeasure options rather than treating most incidents as armed conflict.
International humanitarian law (IHL) applies during armed conflict, including to cyber operations conducted in that context. The International Committee of the Red Cross (ICRC) has emphasized that states should take steps to restrain civilian hacking connected to armed conflicts and has described obligations states should consider to limit harmful civilian involvement.
Because definitions and thresholds aren’t uniformly applied across jurisdictions, domestic responses often rely on existing criminal and national security statutes, which can lead to different enforcement approaches and policy choices between states.
Note: The term “cyberterrorism” is widely used in policy and media, but there is no single internationally settled legal definition used consistently across frameworks. Many discussions, therefore, rely on domestic law and context-specific usage.
Strategies to combat cyberwarfare
Defending against cyberwarfare usually depends on three things working together: state capability (to coordinate national response), private-sector security (because much critical infrastructure and most networks are privately run), and cross-border cooperation (because incidents and evidence often span jurisdictions).
National cyber defense and cyber commands
Many governments have created dedicated cyber organizations to coordinate national defense and military cyber operations. For example, U.S. Cyber Command describes its mission as directing and coordinating military cyberspace operations “to defend and advance national interests,” in collaboration with domestic and international partners, including support to combatant commanders and security of the Department of Defense (DoD) information networks.
Across allied countries, cyber defense institutions are also used to develop policy and operational doctrine, run joint exercises, and share threat information, often through alliance structures and specialist hubs.
International collaboration and policy
Because cyber threats cross borders, international cooperation supports faster investigations, evidence sharing, and coordinated responses. The Budapest Convention on Cybercrime is widely described as a practical cooperation framework that helps practitioners collaborate on cases, including urgent requests that arise in real incidents.
At the global level, in 2024, the UN adopted the United Nations Convention against Cybercrime, which is described as the first comprehensive global treaty on this topic and is intended to strengthen international cooperation, with entry into force after 40 ratifications.
States and other stakeholders also pursue voluntary norms and confidence-building efforts, such as the Paris Call for Trust and Security in Cyberspace, which promotes responsible behavior and cooperation among governments, companies, and civil society.
Regional alliances also matter: the North Atlantic Treaty Organization (NATO) has stated that cyber defence is part of collective defence and that a cyberattack could, in certain circumstances, reach the threshold for Article 5 (an armed attack on one NATO member is treated as an attack on all members) on a case-by-case basis.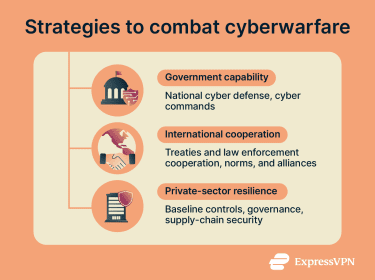
Cybersecurity in the private sector
Businesses are often on the front lines of cyber conflict. The 2023 U.S. National Cybersecurity Strategy calls for rebalancing the responsibility to defend cyberspace by placing more responsibility on the organizations that are most able to reduce risk at scale (such as major technology and cloud providers, software vendors, and critical infrastructure operators), rather than mainly on individual users and smaller organizations.
In practice, that responsibility shows up as a mix of baseline controls and organizational governance. Common safeguards include multi-factor authentication (MFA), regular patching, and reliable backups and recovery plans. Many organizations also manage supply chain risk by assessing and monitoring third-party vendors and service providers, since weaknesses in suppliers can become entry points into larger networks.
Training and awareness programs are another common element, intended to reduce the likelihood of avoidable errors and improve reporting and response.
To keep security consistent as systems grow more complex, many organizations adopt governance frameworks such as zero trust, which focus on limiting implicit trust and continuously controlling access to resources.
Some private-sector initiatives are also trying to curb the commercial market for offensive cyber services. In 2023, Microsoft and the Cybersecurity Tech Accord warned that cyber mercenaries pose a growing risk and promoted industry principles and coordinated action aimed at limiting their harm.
Real-world examples of large-scale cyberattacks
Examining past cyber incidents reveals patterns and consequences. The following examples illustrate how cyber operations have evolved from causing simple disruptions to sophisticated, coordinated campaigns.
Historical incidents
Cyberattacks are not isolated to any specific country; any nation can be a target. While major incidents have been rising globally, there are several important historical attacks that demonstrate the impact of an attack.
- Estonia DDoS attacks (2007): In April–May 2007, Estonia faced waves of DDoS activity that disrupted access to online services, including government and parliamentary sites, media, and banks, over roughly three weeks. The incident is widely treated as a milestone in understanding politically motivated disruption on a national scale.
- Stuxnet (2010): The Stuxnet malware allegedly targeted industrial control systems linked to Iran’s Natanz enrichment facility and is widely cited as the first publicly known malware to cause physical effects on industrial equipment.
- Ukraine power grid attacks (2015): In December 2015, attackers disrupted Ukraine’s electrical grid, causing blackouts. These operations are described as combining network intrusion with the manipulation of industrial control systems.
- NotPetya (2017): The NotPetya malware masqueraded as ransomware but was reportedly designed to destroy data. A U.S. Department of Justice indictment attributed the operation to Russia’s military intelligence service (GRU) and described it as causing nearly $1 billion in losses to the three named victims alone; the malware also spread globally and disrupted major companies.
Recent attacks
Recent incidents show a shift toward operations that can disrupt essential services and large-scale supply chains; many demonstrate the capability of seriously damaging national infrastructure or security.
- SolarWinds supply chain compromise (discovered 2020): SolarWinds is a company that makes IT network management software, including the Orion platform used by many organizations to monitor and manage networks. Attackers compromised SolarWinds’ software build and update process and inserted malicious code into signed Orion updates distributed through normal channels. After customers installed the updates, the attackers could then choose specific networks for deeper access. The U.S. government attributed the campaign to Russia’s Foreign Intelligence Service (SVR).
- Colonial Pipeline ransomware disruption (2021): Colonial Pipeline is a major U.S. fuel pipeline operator that transports gasoline, diesel, and jet fuel along the U.S. East Coast. On May 7, 2021, the company shut down pipeline operations in response to a ransomware attack, contributing to widespread fuel disruption. The Federal Bureau of Investigation (FBI) publicly reported the Darkside group was responsible.
- Viasat KA-SAT satellite network attack (2022): In February 2022, a cyberattack disrupted KA-SAT satellite communications, causing significant outages and spillover effects beyond Ukraine. The EU stated that the timing and impact supported Russia’s military actions and described disruptions affecting users in Ukraine and several EU member states.
- Storm-0558 cloud email intrusion (2023): In July 2023, Microsoft Threat Intelligence assessed that Storm-0558, alleged to be a China-based threat actor, used forged authentication tokens to access user email accounts from a number of organizations, including government agencies and related consumer accounts hosted in Microsoft’s cloud.
Industry-specific cyberwarfare
Different sectors face different risks depending on what their systems enable and how tightly digital services are linked to real-world operations.
In the financial sector, incidents often focus on the disruption of services, theft of sensitive financial data, or compromising institutions whose outages can ripple broadly. The IMF has warned that cyber incidents can create extreme losses and notes that the financial sector is highly exposed, with a significant share of incidents affecting financial firms.
In healthcare, ransomware and other disruptions can affect access to clinical systems and delay care. For example, in 2024, a ransomware incident at Change Healthcare disrupted healthcare operations at a national scale in the U.S., illustrating how attacks on major third-party providers can propagate systemic disruption across a sector.
In shipping, manufacturing, and energy, disruptions can halt the physical movement of goods or essential services. NotPetya’s impact on global logistics is often illustrated by major shipping disruptions and large reported losses. For example, Maersk (a logistics company) publicly estimated over a $200 million loss.
FAQ: Common questions about cyberwarfare
What are the most cited examples of cyberwarfare?
How is cyberwarfare different from cyberterrorism?
How can governments and companies defend against cyberwarfare?
How is AI used in cyberwarfare?
Is cyberwarfare considered an act of war?
Can a VPN protect me from cyberwarfare?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN